By Khalid Raza, President & Founder, Graphiant
Let me ask you something that keeps a lot of CISOs up at night.
How many applications does your enterprise run? If you're a mid-to-large organization, the honest answer is probably somewhere between 200 and 600. SaaS applications alone average over 220 per organization. Add your internally built systems, legacy ERP, partner APIs, custom microservices, and the sprawl of acquired company tech stacks, and the real number is sobering.
Now ask yourself: how many of those applications are protected by post-quantum cryptography?
For the vast majority of enterprises today, the answer is zero.
The Threat That's Already Happening
Most security conversations about quantum computing focus on the future — when will Q-Day arrive? Will it be 2030? 2035? The estimates vary, but they share a common flaw: they treat this as a future problem.
It isn't.
The NSA, CISA, and NIST have all formally warned that adversaries — nation-state actors in particular — are already harvesting encrypted enterprise traffic today, storing it with the explicit intention of decrypting it once quantum computers mature. This is called Harvest Now, Decrypt Later (HNDL). It doesn't require a quantum computer to execute. It just requires patience — and the encrypted data your network is transmitting right now.
Think about what that traffic contains. Intellectual property transfers. Financial transactions. Clinical trial data. Partner contracts. Supply chain details. The things that make your business valuable — all of it encrypted with TLS 1.2, the protocol that Shor's algorithm will crack.
The math of TLS 1.2
Qualys SSL Labs scans of the top 150,000 websites show that 99.9% still support TLS 1.2. Inside enterprise networks, the number is effectively 100% — TLS 1.2 is the default for ERP systems, partner APIs, legacy apps, and custom internal tools built over the past decade. TLS 1.2 uses RSA and ECC key exchanges. Both are broken by Shor's algorithm running on a cryptographically relevant quantum computer.
The standard advice is correct: enterprises need to migrate their applications to NIST-standardized PQC algorithms — ML-KEM (CRYSTALS-Kyber) and ML-DSA (CRYSTALS-Dilithium), standardized in 2024. The question is not whether to do it. The question is how long it takes.
The historical record is not encouraging. The migration from SHA-1 to SHA-256 — a relatively contained cryptographic change — took the industry nearly a decade from the moment NIST published guidance to broad enterprise adoption. The migration away from TLS 1.0 and 1.1, which began in earnest around 2018, still has not fully completed: as of 2024, nearly 28% of websites still supported TLS 1.0.
PQC migration is a larger problem:
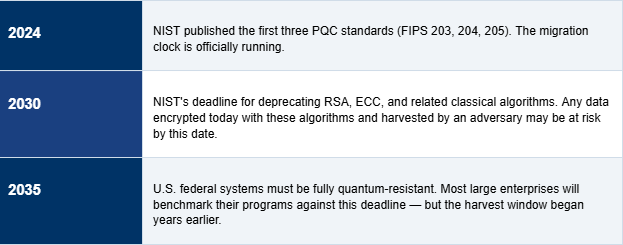
The uncomfortable reality: most enterprises will not complete application-level PQC migration before 2030 at the earliest. NIST's own deadline for U.S. federal systems is 2035. The harvest is happening now. The gap between today and PQC readiness is measured in years. That gap is your attack surface.
Here is what changes when you think about this differently.
Quantum computers will break the public-key cryptography used in TLS key exchange — RSA and ECC. The payload encryption itself (AES-256) is largely quantum-resistant. The vulnerability is in the handshake that establishes the session keys. If you protect the key exchange at the network layer, you protect everything that flows across it — regardless of what the application is doing.
Graphiant deploys a stateless software core at the center of your network, with lightweight edge nodes at every site, every cloud on-ramp, and every B2B partner connection. Every packet entering the Graphiant fabric is wrapped in a PQC-secured tunnel — using NIST-standardized algorithms — at the network layer.
The applications don't change. The servers don't change. The legacy ERP system that won't get a PQC patch for five years is protected anyway. The partner running TLS 1.2 on a system that predates smartphones is protected anyway. The microservice that your team built in 2019 and hasn't touched since is protected anyway.
Graphiant as a PQC proxy — what it protects
All without modifying a single application, updating a single certificate, or waiting for a single vendor patch.
Graphiant's onboarding is software-driven. There is no hardware appliance to rack, no lengthy provisioning process, no change management cycle that stretches across quarters. A lightweight Silicom CPE ships to a site. The stateless core is already running in Graphiant's global fabric. The site connects, authenticates, and is provisioned — in under 60 seconds.
For a 100-site enterprise, a Graphiant deployment covering the entire WAN is achievable in days, not months. For a 1,000-site enterprise, weeks. The PQC protection travels with the fabric — the moment a site is onboarded to Graphiant, its traffic is quantum-safe.
This is not a replacement for application-level PQC migration. That work still needs to happen, and it should. But it is the bridge that eliminates the harvest-now-decrypt-later window while your development teams do the work properly.
Three numbers that frame the problem:
Financial Services
Transaction logs, wire transfer records, and client financial data are high-value targets with multi-decade confidentiality requirements. An adversary harvesting encrypted inter-bank traffic today could unlock it by 2030. Graphiant's PQC proxy protects every transaction flow — internal, partner, and cloud — without waiting for core banking system vendors to ship PQC-ready patches.
Healthcare & Life Sciences
Clinical trial data, patient records, and pharmaceutical IP are subject to regulatory requirements that extend decades into the future. TLS 1.2 on legacy EMR systems and research collaboration platforms is endemic to the industry. Graphiant wraps all of it in quantum-safe encryption at the network layer, irrespective of the application's own cryptographic posture.
Manufacturing & Supply Chain
Partner-facing B2B connections — supplier APIs, EDI systems, logistics platforms — are often the last to receive security updates and the most likely to be running legacy TLS. Graphiant's B2B connectivity service provides PQC-secured partner connections as a managed service, eliminating the harvest window on supply chain traffic.
Government & Defense Contractors
CMMC 2.0, FedRAMP, and the NSA's CNSA 2.0 roadmap are all moving toward mandatory PQC. Graphiant's NaaS architecture, with its native support for NIST PQC standards and sovereign routing controls, provides a compliant foundation that helps contractors begin demonstrating quantum readiness ahead of regulatory deadlines.
Your applications are not quantum-ready. That is not a criticism — it is a statement of fact for essentially every enterprise on earth. Application-level PQC migration is a years-long program that most organizations are just beginning to plan.
But your network can be quantum-ready today.
Graphiant's stateless NaaS architecture, deployed as a network-layer PQC proxy, closes the harvest-now-decrypt-later window across your entire enterprise — every site, every cloud, every partner connection, every application — in hours. Without touching your applications. Without waiting for vendor patches. Without the multi-year migration timeline.
The data is being harvested now. The question is whether your network will protect it.
Ready to close the quantum gap?
Graphiant can deploy PQC proxy protection across your enterprise network in hours. Talk to us about how our stateless NaaS architecture protects every application — internal, cloud, SaaS, and B2B — while your teams work through application-level PQC migration at their own pace. Contact us at graphiant.com.
Resources